Author: Amiram Shachar, Founder and CEO of Upwind
Bio: Amiram Shachar is the founder and CEO of Upwind, the runtime-powered CNAPP helping organizations protect everything they run in the cloud with real-time insights. Prior to founding Upwind, Amiram founded and built Spot.io, the world’s leading cloud optimization organization, which was sold to NetApp for $450 million in 2020.
Kubernetes implementation has risen in usage in popularity due to its affordability, flexibility and scalability, allowing organizations to deploy applications in on-premises, hybrid-cloud or public cloud environments. With this widespread adoption, increased risks and sophisticated threat actors have also come into play, and with that, the need for new and improved methods of protecting Kubernetes.
While focus in recent years has centered on the shift-left security mentality, static analysis of Kubernetes is not enough to sufficiently guard against increasingly advanced threat actors. Instead, organizations should implement security practices that leverage real-time, runtime insights in order to provide continuous Kubernetes security.
Securing Kubernetes
To achieve optimal Kubernetes security, it is crucial to monitor and protect K8s at multiple levels: the control plane and the data plane, which includes infrastructure, applications, and containers.
A compromised Kubernetes cluster can lead to data breaches, service disruptions, and reputational damage. A single Kubernetes cluster can include dozens of applications and entry points, allowing a single breach to quickly escalate beyond the point of entry. By implementing proactive real-time and runtime security measures, organizations can avoid costly security breaches and protect their assets while maintaining compliance.
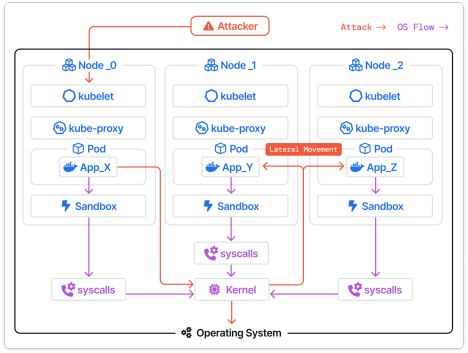
Securing Kubernetes is critical for organizations due to its hybrid-architecture, meaning attackers have more possible areas to exploit. For example, if an attacker finds container vulnerabilities and an attack path, there is a chance they can also find additional vulnerabilities on the cluster level that let them escalate privileges. While one of these vulnerabilities and entry points could be severe, both together on the same cluster could give them expedited access to your Kubernetes and the ability to quickly cause significant damage to your environment.
Kubernetes security is especially critical for organizations, because Kubernetes attacks can often quickly escalate. For example, in a Kubernetes environment a compromised node can become a springboard for attackers to traverse the cluster, compromising other pods and nodes. Once an environment is compromised, it can become susceptible to some of the most common attacks, including cryptominers, escalating privileges, Kubelet manipulations, privileged pods, public access, excessive RBAC and more.
Exploiting Vulnerabilities: The Fastest Path to Attack Kubernetes
Attackers often find Kubernetes attack paths through vulnerabilities that are unknown to organizations, using them as an easy entry point to carry out Kubernetes attacks. There are numerous common methods for attackers to exploit vulnerabilities in Kubernetes. OWASP lists the top 10 most common Kubernetes risks as:
- insecure workload configurations
- supply chain vulnerabilities
- overly permissive RBAC configurations
- lack of a centralized policy enforcement
- inadequate logging and monitoring
- broken authentication mechanisms
- missing network segmentation controls
- secrets management failures
- misconfigured cluster components
- outdated and vulnerable Kubernetes components
From this list, it’s abundantly clear that the majority of organizations can fall victim to one or a number of these risks, often without their knowledge. This highlights the need for organizations to not build securely, but to also understand what is actually happening in their Kubernetes environments at runtime and remediate the most critical risks.
Why You Need to Scan For Kubernetes Vulnerabilities at Runtime
In order to identify critical Kubernetes vulnerabilities, It is essential to scan every running image and pod that runs an application, as vulnerable images can cause widespread damage in the cluster using privilege escalation techniques. While legacy tools have focused on scanning for misconfigurations prior to pushing into live production environments, more robust and continuous scanning is needed to ensure Kubernetes security in dynamic runtime environments.
Prioritizing Kubernetes Vulnerabilities
For example, many legacy security tools scan images during the build phase or when they hit the repository. However, this fails to give a clear picture of which images and CVEs are actively present in live production environments, ultimately creating a noisy environment for security engineers.
Since threat actors can easily exploit Kubernetes vulnerabilities, it is crucial for security teams to understand and fix critical vulnerabilities in their Kubernetes environment that are actually exploitable. The best way to identify and prioritize these vulnerabilities is by scanning images at runtime while they run on the cluster. This gives security teams real-time scanning and an accurate inventory of running images and active, exploitable CVEs, with real-time attachment to their cloud configurations.
In order to address the ever-increasing number of security vulnerabilities in applications, security teams must know where a vulnerability is (e.g., in production vs. a QA/Test environment), and whether the service has been actively communicating with the Internet or targeted by any attacks. This context makes a substantial difference in determining whether it is worth prioritizing remediation or actively mitigating potential exploits.
There are numerous factors that should be considered when prioritizing Kubernetes CVEs, including:
- The environment of the service (production, test or sandbox)
- Whether the vulnerable package associated with the service is actually in use ● Whether the service is actively communicating or exposed to the Internet and in which ports
- Whether the service has been attacked recently
- Whether the attack environmental conditions are met to indicate if the vulnerabilities are actually exploited in the specific service.
How to Detect Kubernetes Threats & Attacks
In addition to executing an effective vulnerabilities prioritization and management strategy, organizations must also conduct intelligent threat detection. Containers are dynamic and versatile, ephemeral by nature, and perform multiple actions – making them an attractive target for threat actors to exploit and perform malicious operations.
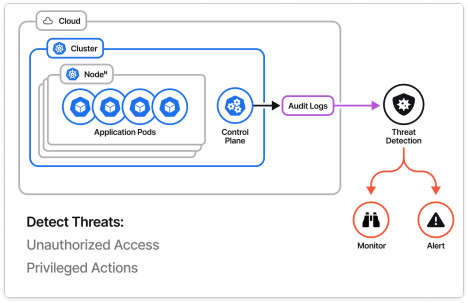
Threat intelligence streams are needed to identify and protect from advanced malware attacks across executable files, running processes and even fileless (in-memory) malicious code. A comprehensive intelligent threat detection strategy will also include detections of malicious egress, observing Internet ingress and egress traffic in a cloud environment to ensure that no egress traffic goes to malicious IPs and domains.
To Secure Kubernetes, You Need Runtime Data
While we have established the importance of securing Kubernetes during runtime at the infrastructure, application and container levels, the next question is how to best monitor these environments to avoid potential security breaches.
The best option for pod and container monitoring is leveraging the Linux kernel and eBPF agents that give detailed, real-time insights. eBPF is an open-source technology integrated into the Linux kernel that has become popular in recent years, offering lightweight and detailed monitoring capabilities on a level that was previously unavailable.
With eBPF, organizations can monitor process execution, system calls, file access, network layer communication, and data access within Kubernetes deployments. This provides security leaders with detailed runtime insights into their Kubernetes environment, allowing them to ensure the integrity of the containerized workloads and receive visibility and deep context of Kubernetes threats and vulnerabilities at any given moment.
In conclusion, securing Kubernetes with real-time, runtime insights is a necessary measure in order to maintain organizational security. By leveraging runtime insights, organizations can detect threats and respond to them in real time, identify the risks that are actually exploitable in their Kubernetes environment and prioritize their most critical risks and threats.
Join us at KubeCon + CloudNativeCon North America this November 6 – 9 in Chicago for more on Kubernetes and the cloud-native ecosystem.







